menu
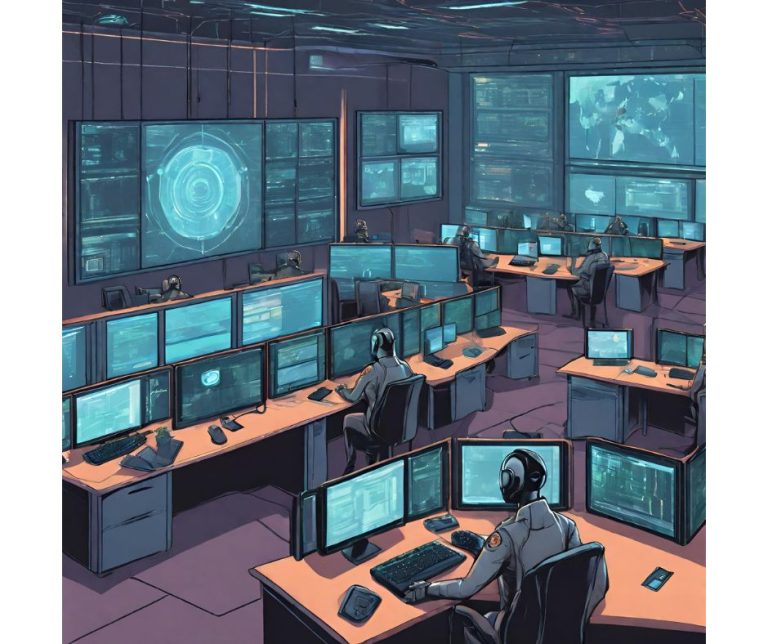
Security Operations as a Service (SOCaaS)
In the ever-evolving landscape of digital threats, safeguarding your organization is not just a priority; it’s a necessity. we understand the challenges of maintaining robust cybersecurity defenses. That’s why we proudly introduce our Security Operations Center (SOC) as a Service – an innovative solution designed to fortify your digital resilience.
Lower cost than on-premise SOC
While we prioritize cost efficiency, we never compromise on the quality and effectiveness of our cybersecurity services. Rest assured, your organization benefits from top-tier threat detection, rapid incident response, and continuous improvement, all within a budget-friendly framework.
Proactive Threat Detection:
Our state-of-the-art platform employs advanced algorithms and real-time monitoring to detect and neutralize potential threats before they escalate.
Rapid Incident Response
Time is of the essence in cybersecurity. Benefit from our automated incident response workflows and expert team, ensuring swift and effective action in the face of security incidents
Pay-as-You-Grow
Our flexible pricing models ensure that you pay for the services you use. As your organization expands, so can your cybersecurity coverage, all without the burden of significant upfront costs
SOC Levels we provide
SOC Manager
The SOC Manager oversees the Security Operations Center, providing strategic leadership. They develop cybersecurity policies, collaborate across departments, and ensure effective incident coordination, communicating insights to executive leadership
Security Analyst Tier 1 - Triage
Tier 1 Analysts conduct initial analysis and triage of security alerts. They distinguish false positives from actual incidents, perform basic incident response actions, and escalate confirmed incidents to higher-tier analysts.
Security Analyst Tier 2 - Incident Responder
Tier 2 Analysts delve into confirmed security incidents, conducting in-depth investigations. They execute incident response plans, collaborate with IT and business units, and document incident details for continuous improvement
Security Analyst Tier 3 - Threat Hunter
Tier 3 Analysts are proactive threat hunters, identifying potential threats not caught by automated systems. They analyze advanced persistent threats, develop new detection methods, and collaborate with threat intelligence teams to stay ahead of emerging risks.
Team Experts

What our clients have to say about us
"Exceptional expertise in penetration testing! Their thorough assessments identified critical vulnerabilities, and their actionable recommendations significantly bolstered our cybersecurity defenses. A trusted partner for safeguarding our digital assets."
An Airline CompanyDirector, Information Security
"Red teaming excellence! Their simulated attacks were incredibly realistic, providing valuable insights into our security posture. The collaborative approach and detailed reporting showcased their commitment to strengthening our resilience against advanced threats."
A Retail CompanyCISO
"Unparalleled application security assessments! The team demonstrated an in-depth understanding of our software landscape, uncovering vulnerabilities that were previously overlooked. Their tailored solutions and proactive guidance have been instrumental in enhancing our application security."
United States Government EntityDirector of Cyber Security
"A game-changer in penetration testing! Their comprehensive methodology not only detected vulnerabilities but also provided practical solutions for mitigation. Their attention to detail and commitment to continuous improvement make them a standout choice for any organization serious about security."
A Hospital ChainVP, Information Security
"Red teaming that goes beyond expectations! The team's ability to emulate real-world attacks and expose weaknesses in our defenses was truly eye-opening. Their insights have been pivotal in refining our incident response strategies and fortifying our overall security posture."
A BankCIO
"Exemplary application security expertise! The team's proficiency in identifying and remediating vulnerabilities in our software applications has been crucial to our risk management efforts. Their clear communication and tailored recommendations showcase a commitment to securing our digital assets effectively."
A Crypto WalletCEO
Previous
Next
